Social engineering refers to the manipulation of individuals or groups to gain unauthorized access to information, systems, or physical locations. It is a technique often employed by malicious actors who exploit people’s psychology, beliefs, and vulnerabilities to trick or trick individuals into performing actions that benefit the attacker.
Some Real incidents of Social Engineering attacks
Kevin Mitnick Case
Description: Kevin Mitnick, one of the most notorious hackers, was involved in a series of social engineering incidents in the 1990s. A notable incident occurred when he gained unauthorized access to the computer systems of Pacific Bell and Digital Equipment Corporation. Mitnik exploits human vulnerabilities by impersonating employees and manipulating them into revealing sensitive information.
History: Mitnick’s social engineering exploits spanned several years, during which he used a variety of techniques such as trickery and exploits to gain access to confidential data. His actions led to significant financial losses for the target companies and eventually landed him in legal trouble.
Lesson: The Kevin Mitnick case highlights the importance of employee awareness and safety training. It emphasizes the need for organizations to educate their employees about social engineering techniques, encourage skepticism, and implement strict protocols to prevent unauthorized access.
Reference: What we learnt from the FBI’s former most wanted hacker, Kevin Mitnick
Target Data Breach
Description: In 2013, Target, a major retail corporation, suffered a massive data breach that exposed the personal and credit card information of approximately 110 million customers. The breach began with a social engineering attack on a third-party HVAC contractor working with Target. The attackers sent phishing emails to the contractor, which allowed them to gain access to the target’s network.
History: Attackers used spear phishing emails to compromise the credentials of an HVAC contractor who had access to the target’s systems. Once inside, they migrate laterally within the network, eventually accessing point-of-sale systems and stealing customer data.
Lesson: Target breach highlights the importance of supply chain security. Organizations need to ensure that their third-party vendors and contractors adhere to strong security protocols. Regular security audits, employee training, and strict access controls can help prevent social engineering attacks from compromising networks.
Reference: WARNINGS (& LESSONS) OF THE 2013 TARGET DATA BREACH
OPM Data Breach
Description: In 2015, the US Office of Personnel Management (OPM) suffered a significant data breach that exposed the personal records of approximately 21.5 million current and former federal employees. The breach was the result of a social engineering attack targeting a contractor working for OPM.
History: Attackers sent spear-phishing emails targeting OPM employees and contractors, tricking them into revealing their login credentials. Once attackers gain access, they exfiltrate sensitive data, including Social Security numbers and background investigation records.
Lessons: The OPM breach emphasized the importance of continuous monitoring and detection of unusual activity. Organizations should implement multi-factor authentication, conduct regular security awareness training, and use advanced threat detection tools to identify potential social engineering attacks.
Reference: The OPM Data Breach: How the Government Jeopardized Our National Security for More than a Generation
Snapchat Phishing Attacks
Description: In 2016, attackers launched a phishing attack targeting Snapchat, a popular social media platform. Attackers impersonated Snapchat’s CEO and sent an email to an employee requesting salary information for current and former employees. Employees fall victim to phishing emails and attackers gain access to sensitive employee data.
History: A phishing email successfully tricked an employee, who disclosed salary information. This incident highlights the effectiveness of social engineering attacks through impersonation and the need for strong email security measures.
Lesson: Organizations need to implement strong email security protocols, including anti-phishing measures, employee training on identifying phishing emails, and verification procedures for sensitive data requests. Additionally, applying a culture of skepticism and verifying requests through alternative means can help prevent successful social engineering attacks.
Reference: Snapchat Employees Fell for a Phishing Scam, Here’s How They Responded
Bangladesh Bank Heist
Description: In 2016, cybercriminals attempted to steal nearly $1 billion from Bangladesh Bank by compromising the bank’s computer systems. The attackers used social engineering techniques, including spear phishing emails, to gain access to the bank’s network and manipulate SWIFT’s financial messaging system.
History: Attackers sent spear phishing emails containing malware to Bangladesh Bank employees. Once the malware was installed, the attackers gained control of SWIFT credentials and initiated fraudulent transactions totaling $81 million. However, most transactions were blocked, preventing outright theft of funds.
Lesson: The Bangladesh bank heist highlights the need for strong security measures within financial institutions. Implementing multi-layered security controls, conducting regular security audits, and providing extensive training on social engineering attacks is critical to protecting sensitive financial systems. In addition, organizations should strengthen collaboration with industry peers to share information and best practices to combat social engineering threats.
Reference: That Insane, $81M Bangladesh Bank Heist? Here’s What We Know
Social Engineering Techniques
Social engineering techniques can take many forms, including:
- Impersonation: An attacker creates a scenario or excuses to gain the trust of a target, such as impersonating a colleague, service provider, or authority figure to gain information or access.
- Phishing: An attacker sends fraudulent emails, text messages, or other forms of communication, posing as a legitimate entity, to trick the recipient into revealing sensitive information such as passwords or financial details.
- Luring: The attacker offers something enticing, such as a free download or a physical device, to entice the target to perform an action that compromises security, such as clicking a malicious link or inserting an infected USB drive.
- Tailgating: An attacker follows closely behind an authorized person to enter a restricted area by exploiting the natural tendency to hold the door open for others.
- Impersonation: An attacker pretends to be someone else, through physical appearance, phone calls, or online interactions, to trick individuals and manipulate them into providing sensitive information or access.
Social engineering attacks can target individuals, organizations, or even entire societies. They exploit the weaknesses of human nature such as trust, curiosity, and willingness to help to bypass technological security systems. Effective social engineering attacks can result in financial losses, data breaches, identity theft, or unauthorized access to systems.

How to protect yourself and your organization from social engineering attacks
To protect, prevent, and protect yourself and your organization from social engineering attacks, you can implement the following measures:
Education and Awareness
- Train employees on social engineering techniques, common attack vectors, and how to identify suspicious activities.
- Conduct regular security awareness programs to reinforce best practices and create a security-aware culture.
- Educate employees about the importance of vetting requests for sensitive information and the risks associated with indiscriminate information sharing.
Strong authentication and access control
- Implement multi-factor authentication (MFA) to access sensitive systems and resources.
- Enforce strong password policies, including changing passwords regularly and using complex, unique passwords
- Limit user access to only the resources required for their job role, reducing the attack surface for potential social engineering attacks.
Strong email security
- Deploy anti-phishing solutions that can detect and block suspicious emails before they reach users’ inboxes.
- Implement email filtering and scanning processes to detect and prevent malicious attachments or links
- Train staff to check emails for signs of phishing, such as unusual requests, spelling errors, or suspicious email addresses.
Physical Security
- Implement strict access control systems for physical premises, including secure entry systems, employee ID badges, and visitor management protocols.
- Promote a culture of caution about tailgating and the importance of reporting any suspicious activity or unknown persons in restricted areas.
Incident Response and Reporting
- Establish clear incident response procedures to immediately handle suspected or confirmed social engineering attacks.
- Encourage employees to report any incidents or potential security breaches to the appropriate channels.
- Maintain a strong communication network to disseminate information and respond quickly to emerging threats.
Regular safety assessments and audits
- Conduct periodic security assessments to identify vulnerabilities and weak points in systems and processes.
- Perform regular penetration testing to assess the effectiveness of security controls and identify potential social engineering vectors.
- Engage external security professionals to perform comprehensive audits and provide recommendations for improvement.
Vendor and supply chain security
- Evaluate the security practices of third-party vendors and contractors, especially those with access to sensitive data or systems.
- Incorporate security requirements into contracts and agreements with vendors, ensuring they adhere to industry-standard security protocols.
- Regularly review and update vendor access privileges and monitor their activity for any suspicious behavior.
Remember, preventing and protecting against social engineering attacks requires a combination of technical measures, employee education, and a security-conscious culture. It is an ongoing effort that demands constant vigilance, regular training, and staying up-to-date with emerging social engineering techniques.
Choose RedNode
With over a decade of relentless commitment to protecting the cyber world, RedNode has emerged as an undisputed leader in cyber security. Renowned for their extensive expertise and invaluable experience, they offer an attractive solution to combat the growing threat of social engineering attacks.
RedNode’s highly skilled team consists of seasoned professionals who have successfully thwarted numerous cyber threats, stay ahead of the curve and constantly refine their strategies. By choosing RedNode as their trusted training partner, individuals and organizations can access a wealth of knowledge tailored to countering social engineering attacks.
RedNode’s training programs are designed to empower individuals with the tools and skills necessary to recognize, prevent, and mitigate social engineering threats. Training modules incorporate cutting-edge methodologies, real-world case studies, and interactive simulations, fostering a proactive and resilient cyber security mindset.
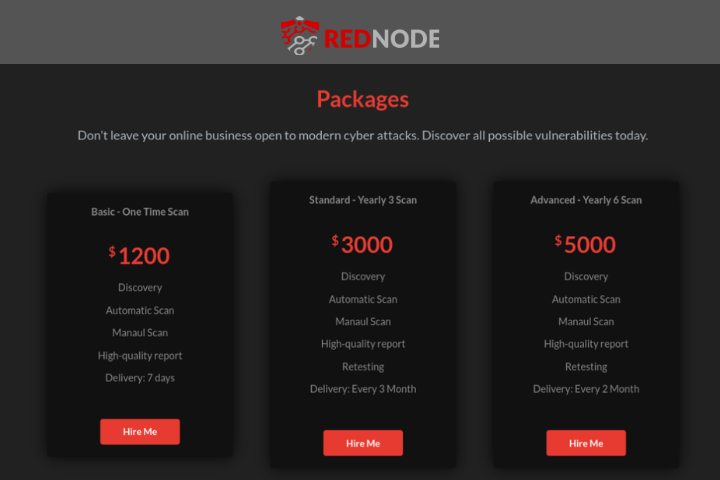
By enlisting RedNode’s expertise, clients can benefit from an unparalleled level of guidance, gaining practical insight into social engineering techniques, psychological manipulation, and best practices for protecting sensitive information. RedNode’s extensive training empowers participants to confidently and effectively detect and respond to social engineering attacks, significantly reducing the risk of falling victim to such malicious tactics.
In a world where cyber threats are pervasive, hiring RedNode as a go-to training partner ensures that individuals and organizations can strengthen their defenses against social engineering attacks, creating a secure and resilient cyber landscape for years to come.
Connect with RedNode.